

Willow vs. Lunar MCPX: Enterprise Platform vs. OSS Control Plane
MCPX is an open-source control plane with YAML config and Prometheus metrics. Willow is an AI governance platform with shadow AI detection, unified build & runtime guards, infrastructure-as-code via GitHub, and a plugin marketplace—proven at 5,000+ employees.
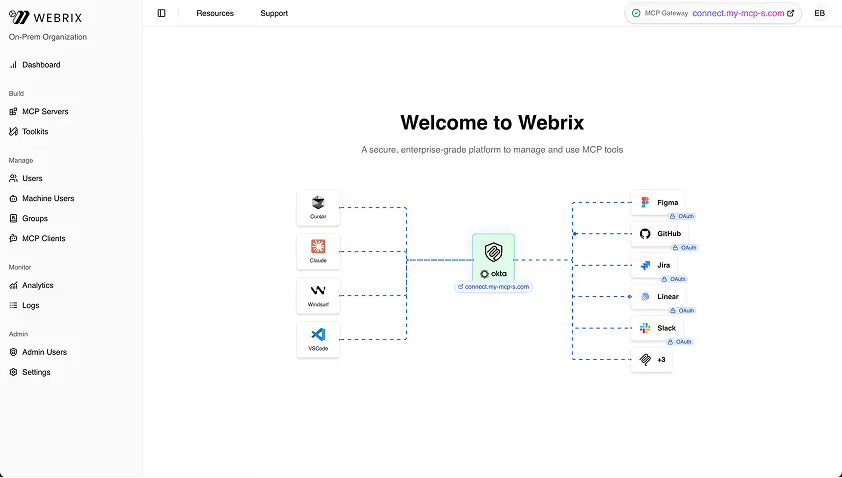
Willow Admin Console
AI governance platform. Shadow AI detection, unified guards, plugin marketplace, infrastructure-as-code, and 5,000+ employee deployments.
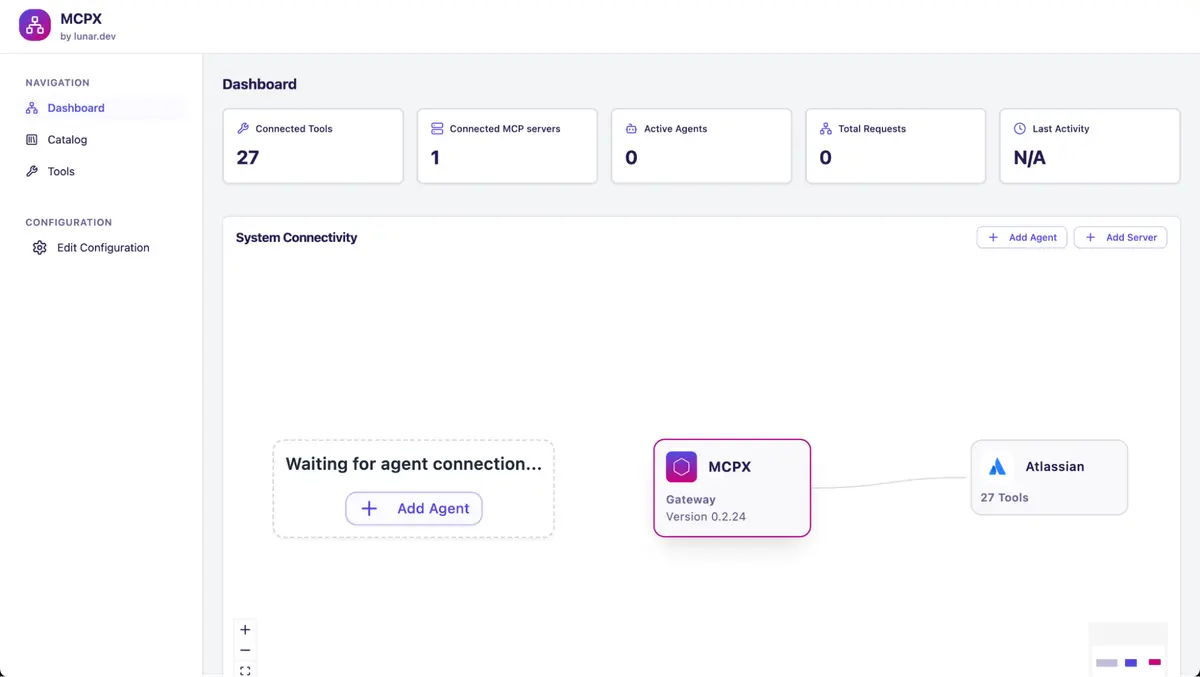
Lunar MCPX Control Plane
Open-source MCP control plane. YAML-based configuration, Prometheus metrics, and 13 pre-built MCPs.
The Bottom Line
MCPX is open-source with YAML config and Prometheus observability for DevOps teams. Willow provides shadow AI detection, unified build & runtime guards, infrastructure-as-code governance, and a plugin marketplace at enterprise scale.
Best for Willow
Enterprises needing shadow AI detection, unified guards, and infrastructure-as-code governance at scale
Best for Archestra
DevOps teams wanting open-source with YAML config and Prometheus observability.
Key Differentiator
Willow offers shadow AI detection, unified guards, and infrastructure-as-code governance. MCPX provides open-source infrastructure with YAML config.
Give your agents a Basecamp
Feature Comparison
Who Each Solution Is Best For
Willow is Best For
Enterprises needing employee enablement and fine-grained governance. Ideal if you:
Cloudflare MCP Portals is Best For
DevOps teams wanting open-source with infrastructure control. Ideal if you
Deployment & Infrastructure
Web UI vs. YAML configuration approaches.
Willow offers offers managed deployment:
- SaaS or On-Prem: SOC 2 compliant infrastructure
- Air-Gapped: Fully isolated environments
- Web Admin UI: Visual configuration
- Rapid Setup: Deployments in days
MCPX provides open-source infrastructure:
- Open-Source Core: Free for personal use
- YAML Config: Infrastructure-as-code approach
- Self-Managed: You handle deployment and updates
- DevOps-Centric: Requires technical expertise
Security & Governance
Enterprise identity vs. infrastructure-level controls.
Willow delivers enterprise governance:
- Shadow AI Detection: Discover unmanaged MCPs, skills, and AI agents org-wide
- Browser Extension: Enforce governed AI usage wherever employees work
- Unified Guards: Build & runtime policy enforcement, easily extensible
- Audit Trails: SOC 2 compliance logs
Cloudflare focuses on Zero Trust access:
- API Key Auth: Token-based access
- ACL Per Tool: Access control lists
- Consumer Tags: Tag-based management
- Infrastructure Policies: General enforcement
Connectors & Extensibility
Pre-built catalog vs. DIY approach.
Willow provides 100+ connectors:
- Plugin Marketplace: Skills, commands, MCPs, hooks—all in one place
- GitHub/GitLab Sync: 2-way sync for Claude, Codex, Cursor integration
- API-to-MCP: Convert any REST API
- CLI Access: Single CLI installs your entire gateway in any IDE
MCPX offers focused options:
- 13 Pre-built MCPs: Core connectors
- Tool Customization: Extend and modify
- Bring Your Own: Build additional MCPs
- Lightweight Focus: Core aggregation
Employee Enablement
Self-service portal vs. developer infrastructure.
Willow enables self-service:
- Employee Connect Panel: Browse MCPs, skills, commands, and plugins
- Machine Users: Agent-to-agent automation
- One-Click Connect: Cursor, Claude, VS Code
- No IT Bottleneck: Self-service discovery
MCPX focuses on infrastructure:
- No Employee UI: Technical infrastructure only
- Developer-Centric: Config file management
- API-First: Integration via APIs
- IT Setup Required: DevOps intervention needed
Guardrails Granularity
Fine-grained vs. infrastructure-level governance.
Willow offers fine-grained policies:
- Unified Guards: Build & runtime enforcement in one layer
- Per-Agent: Policies for Cursor, Claude, Codex, custom
- Per-MCP: Access and limits per connector
- Easily Extensible: Add custom guards out of the box
MCPX provides infrastructure controls:
- General Policies: Infrastructure-level enforcement
- ACL Per Tool: Access control lists
- Consumer Tags: Tag-based management
- DIY Granularity: Build custom as needed
FAQS
Everything you need to know about Willow compared to Archestra
Everything you need to get your Basecamp running.
Your agents are already in the wild.
Give them a Basecamp. Go from AI chaos to AI work, in minutes.




